[Edit 8/13/15] – Here is how the old version 1.9 cmdlets in this post translate to PowerView 2.0:
- Invoke-StealthUserHunter -> Invoke-UserHunter -Stealth
- Invoke-SearchFiles -> Find-InterestingFile
- Get-NetFileServers -> Get-NetFileServer
My boss comes from a red teaming background; I do not. When I started to move beyond simple pentests and absorb his more advanced tradecraft, I was amazed that I hadn’t heard of much of it before. I wondered why there wasn’t more public information on these powerful tactics, techniques, and procedures. Now that I have a bit better of a grasp on red teaming, I think I might know why.
One of the big differentiators between a pentest and a red team engagement is that pentests tend to have fewer people and a more constrained timeframe. There are few organizations that can afford to have teams of dozens of people working on a single op for months at a time. Teams that have the luxury of these kind of resources are usually internal groups for large corporations, or a part of some government entity. Many components of red team tradecraft have traditionally usually consumed a large number of man hours to accomplish and thus have stayed relegated to the realm of these specialized teams. It often didn’t make sense to talk heavily about tactics that few people could use on assessments.
At the Adaptive Threat Division, one of our key philosophies is to push down red team tradecraft into time-limited engagements. A big part of this is building toolsets that automate actions that used to have to be done manually. Another big component is sharing as much knowledge as we can with the community. We believe that the more testers up their tradecraft game, the better we can all start to simulate more advanced attackers and the safer all of our clients will be. We want to do our small part to help bridge the gap between pentesting and traditional red team operations.
I want to highlight three main tradecraft areas that I feel our group has made big strides in pushing down to our pentests over the last year. This will be similar to the “Passing the Torch: Old School Red Teaming, New School Tactics?“ presentation that my boss and I gave at Derbycon ’14, but with some expanded information and additional context. I am by no means claiming that we are the only ones who have made advances in these areas, and this is by no means a complete list of red team tradecraft topics.
Network Situational Awareness
One of the first steps forward we had was the creation of PowerView. This was originally prompted by a client who locked down their corporate machines by disabling all “net *” commands for normal users. We soon expanded its functionality with a port of Rob Fuller‘s netview.exe project and have continued adding features over the past several months.
There are now several functions in PowerView that allow you to search for additional machines where you current user has local admin access. These are covered in detail in “Finding Local Admin with the Veil-Framework”. PowerView can also query the members of the local administrators group on a remote machine with Get-NetLocalGroup. This can be extremely useful when dealing with KB2871997, the “pass-the-hash” patch.
But by far the most useful feature in PowerView we’ve used are its user-hunting capabilities. The Invoke-UserHunter and Invoke-StealthUserHunter cmdlets let us locate target users in a network in a fraction of the time it used to take us. There’s more information in the “Hunting for Domain Users With the Veil-Framework” post. These functions, along with other hunting methods are also covered in depth in the “I Hunt Sysadmins” article that accompanied a Shmoocon ’15 firetalk (with the video here). An expanded version of that talk was given at BSides Austin 2015.
Domain Trusts
A year and a half ago, we almost never checked out Windows domain trusts on a pentest. The only tool we had at our disposal was nltest, and most of us didn’t understand domain trusts too well, nor their offensive implications. Domain trust abuse was something we were vaguely aware of, but assumed that it resided in the world of big budgets and long timeframes.
Things have definitely changed. We now enumerate and abuse domain trusts on the majority of our network tests. A big reason for this has been the continued development of PowerView with the addition of domain-trust centric features. There are several features in PowerView that allow for the enumeration of trusts, and most functions accept a “-Domain X” argument to operate across a trust.
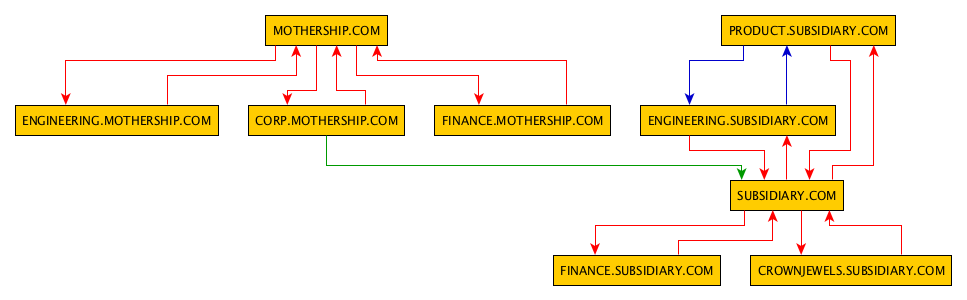
Justin Warner’s (@sixdub) tool DomainTrustExplorer marked another big evolution point. It brings network graph analysis tools as well as GraphML generation to the table. This let us start to build interactive visualizations of the sometimes massive domain meshes we’re operating in.
We’ve also tried to publish quality information on domain trusts. The “Trusts You Might Have Missed” post is a general overview of domain trusts from an offensive perspective. It was researched and written so we could gain a better understanding of trusts and their ability for abuse. Justin’s “Nodal Analysis of Domain Trusts – Maximizing the Win!“ post covers the the visualization and analysis of domain trusts from an analytical perspective. The “Domain Trusts: Why You Should Care“ post brings it all together, providing a step-by-step case study for the enumeration, analysis, and abuse of the trusts in a fictional domain.
These new bits of knowledge and capabilities have allowed us to automate a process of domain abuse that used to be effort intensive. What used to take days to weeks for a team to execute can now be done in a short afternoon.
Data Mining
My boss likes to joke that data mining is how red teams would break new people. The first time I was on a red team engagement, I spent days searching through plaintext directory listings of a fileserver we gained access to. I quickly began to understand that he wasn’t actually joking. Data mining is actually where you’re going to spend the majority of your time on an advanced engagement. Access is (relatively) easy, finding the specific crown jewels for an organization can be a lot more difficult.
We then started looking into using PowerShell for our file server triage. The result was “File Server Triage on Red Team Engagements“, which detailed how to generate easily sortable .csvs of interesting files. This was significantly more effective than grepping dir /s.
These features were then incorporated into PowerView. Invoke-SearchFiles will automate the messy PowerShell one-liners, and Invoke-FileFinder will automate this crawl and search across a network. Get-NetFileServers, which will extract unique file servers from Active Directory user data, functions as a nice complement. There’s a post about these features and their use titled “Hunting for Sensitive Data with the Veil-Framework“.
The newest developments take this all one step further. The Invoke-MassSearch script in Veil’s PowerTools allows you to query the Windows Search Index on remote servers using a combination of WMI, PowerShell, and a temporarily hosted local web server. This lets you search user workstations for files with specific keywords within them, not just a part of their filename. The post describing this process is “Mining a Domain’s Worth of Data With PowerShell“.
Going forward, one of our big goals is to further introduce the idea of data analytics and operational intelligence more into our workflow. Things like nodal analysis and offensive event parsing have helped push us forward, and we have a few more ideas on the horizon that we think you’ll find interesting.
Wrap Up
This past year represents a substantial step forward in our tradecraft. Being able to quickly perform lateral spread, hop through multiple domains, and find a company’s crown jewels in a network of thousands of computers on a pentest that only lasts a few days gives you some impressive results. We hope that other pentesters find these tools and techniques as useful as we have.
Pingback: Raphael’s Magic Quadrant | Strategic Cyber LLC
Pingback: Active Directory Kill Chain Attack 101 – syhack